Be honest: How secure are your WordPress installations? Securing WordPress has in the past years always been an after-thought or for the very big and professional blogs. Probably 90% has no other protection then the basic anti-spam protections like Akismet, which is really really needed.
With WordPress being on the rise as one of the most important CMS-systems so come the security flaws and problems. I’m not saying WordPress is unsafe since the core seems to be quite holding up to all the pressure. The Achilles’ heel seems to be the plugins. Which is also one of the most important features. Let me set out a few basic protection strategies to prevent bad people from breaking in.
1. Make sure to cover the basics
As a basis, everything in your online life the basics should be well secure. That means get rid of the default ‘admin’ user, but give it some other name. Do away with your weak passwords and make they are not easily guessable. You will prevent quite a lot of traffic if your wp admin isn’t on the default location. Many people also say that you should change the prefix of the database tables. I guess I can’t hurt, but if any script can reach there I’d say you are already messed. And hooray-hooray for most of these things (and some more) there are plugins for. Like I-themes better security. Some open doors related to WordPress security can also be found here.
Another plugin that should be mentioned here is Bulletproof. It depends on your needs which one is better. They overlap, but not in all cases.
2. Keep updated!
It sounds obvious in times of automatic updates, but it’s vital everything ( including plugins! ) is updated regularly. Unfortunately updating also tends to break things every now and then. If you are not very tech savvy, it would be wise to get a support contract. It certainly beats the costs of a clean-up after being hacked.
3. Be more careful with plugins
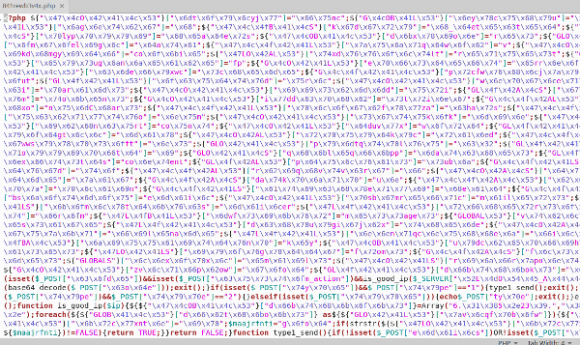
Did you ever check the source code of any plugins? Or even the author’s website? The truth is that WordPress offers a great ‘n easy plugin system where installing one is just as easy as typing the name. To get a plugin in this repository is equally not that difficult.
I’ll take my plugins as an example. I registered them and then got access to the repository of my plugins where they are stored. They are checked when initially sending them, but if I decide on evil I could enter some malicious code now, update them and in a few hours it would spread over tens ( being modest here ) of installations. Imagine what would happen if a big plugin developers’ computer would be hacked…
And maybe the developer is not a bad person, but just a novice coder starting out experimenting with WP plugins and sharing them. There is some bad code out there…
Never forget that when installing a plugin you basically give somebody you don’t know full access your system.
Judging plugins
When considering to use a new plugin look at their status in the plugins directory. For instance how many downloads, how well the plugin is maintained ( look in the support forum ), the website of the author etc. It’s all non-conclusive but gives an impression on the status of this plugin.
I consider a plugin risky if it designed to function in the field of communication to the outside. Things like sending mail (newsletters), connecting social media, taking over login functionality, payment systems or external website integration. Be extra sure to check the code and never use solution that has not (yet) proven themselves unless you have very good reason for that. These plugins are targets for spammers alike, and bad coding can very easily result in all sorts of attacks.
If your site is important, your income depends on this and you don’t really know, it would be good to hire an expert to check it for you.
Removing plugins
Go light on the amount of plugins you are using. Try to keep it at a minimum ( good for performance as well ), de-active and uninstall plugins you are not using. Why keeping the risk for no good reason?
4. Preventing doom and zero-days
A zero-day is an exploit that is so new it might be fully unknown still, even to the developer or there was no time to fix it yet. This kind of problem is clearly on the rise in WordPress and is cause for concern. I recently had a case where a customer was booted off their hosting plan for sending spam (without knowing it ).
This happened to at least another 50.000 sites via the highly used newsletter plugin ‘mailpoet’. Another ( not zero day, but worriesome ) security flaw was in the even more popular ‘revolution slider’ which offers your database details before a certain version.
If you did all the other steps there are few things you can do about this. Still your site is really important. There are services out there like WordFence ( free ) which scans for these type of exploits. Or ( I never used this ) more expensive like securi.
Consider that a site is never finished and needs regular maintanance, just like cars or they will break. If you don’t have to time or knowledge to stay updated on what’s out there, have it do it for you. Don’t become one of the people in panic on the supports forums because they site went down the shitter.
Conclusion
It’s really time to take WordPress security more serious then before since it happens more and the consequences are higher. In general, after applying all the tricks from section 1 ( hardening ), keeping updated, installing one or two (depending on the features) security plugins your site will be rather secure and certainly much more then the other sites out.
And lastly, don’t think it can’t happen to you. Have your engineer standing by knowing what to do when doom sweeps by.
What are your tricks to stay secure with WordPress? Share your WordPress security tips and stories in the comments!
Tags: exploits, plugins, security, updating, zero day
'float:left')); ?>
